Differences between OS and RTOS:
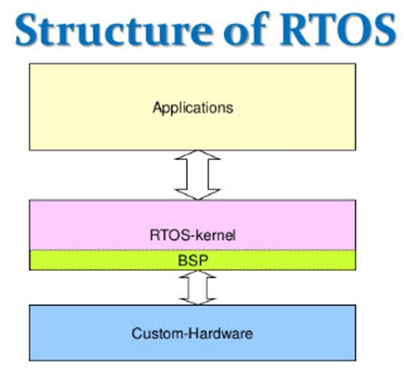
Flowchart Explaining Structure of a typical Realtime Operating System
Operating systems are the interface between the hardware of the system and the applications running on the system. A computing environment with the capacity to respond to events within a strictly defined time frame is presented by real-time operating systems (RTOS). Modern embedded systems for particular domains (like aerospace, industrial control, defense, and medicine) contain safety-critical programmes whose failure would have disastrous consequences. These systems use RTOS instead of general-purpose operating systems to function in challenging and dynamic environments. In the computers we use General Purpose Operating Systems (GPOS) while in embedded systems we use Real Time Operating Systems (RTOS).
When the general-purpose systems such as the desktop
computer is turned on, the general-purpose operating system takes the control
of the desktop machine and then allows the user to run the application. In
desktop computers the user application program separately compiles and links
from the general-purpose operating system. In an embedded system usually
embedded software links with RTOS. At the boot up time, embedded software gets
control first and then it then starts the RTOS.
How is RTOS vulnerable?
RTOS
is heavily used in Embedded system networks as it provides much needed
flexibility in resource management, task scheduling and also provide security
to the system. A poorly designed RTOS that is deployed over a network system
can exploited. An example of an attacker attempting to access private data
that is sent across the network. This method is called data sniffing. If
appropriate encryption techniques are not used, the attacker may be able to
sniff the sensitive data once they have gained access to the network. While
monitoring the transmission, a hacker may get all the information and control
commands, which they could then use to transmit erroneous messages. The
integrity of the data transmitted over the network may likewise be compromised
by an attacker tampering with it. It is possible to make the saved data on the
remote servers a target. A system's memory and processor resources can be
managed by the operating system. If the Operating System is not created with
security in mind, it will always be open to attack and incapable of stopping and
limiting the harm caused by unauthorised access. The system's availability,
validity, confidentiality, and integrity may all be jeopardised by the
attacks. And that's the reason built in security for RTOS are now widely
employed in all sectors of society where it is necessary to protect linked
devices' performance. These sectors include, among others, linked houses,
connected medical equipment, vital industrial/infrastructure control systems,
and connected cars.
One
of the most frequent and perhaps most harmful forms of attacks on contemporary
computer system networks is code injection. These attacks operate by installing
and running arbitrary code on the targets' computers. Typically, the goal is to
take over the machine's programme counter (PC). This gives the attacker the
ability to alter the order in which instructions are executed and trick the
computer into running malicious code that the attacker has added. This injected
code may be natively executable machine code, intermediate byte-code, or source
code for an interpreted scripting language. Such code may be created for an
instant attack, where it runs immediately (such as stealing user session data
or running a modified SQL query), or it may run later. One such peculiar
instance included an EV charger. By switching the "Branch if equal"
(BEQ) assembly instruction to "Branch if not equal" (BNE) in debug
mode, it was possible to get around the password authentication process for EV
chargers. This gives the attackers the ability to enter false passwords and yet
access the system code of the device.
How are these security concerns dealt in modern RTOS systems?
Use of Multilevel Security Method:
A
highly favoured approach for resolving security challenges is the Multiple
Independent Level of Security method. It primarily operates on the
divide-and-conquer approach, where a process is separated into numerous
independent levels and security policies are applied to independent kernels.
This prevents hackers from breaking the system and isolates the problem,
ensuring that the failure of one partition won't have an impact on the
other.
Use of secure Authentication framework:
A secure user identification and authorisation method are used in the RTOS system to confirm a user. The embedded device is possibly accessible by unauthorised users if they are not correctly identified and authenticated. An embedded device's user accounts shouldn't be static in nature. To prevent automated harmful assaults, features that allow for the separation of user identities for internal web management, internal console access, as well as remote web management and remote console access, should be available. For all services, all access must be permitted and users must only have the minimal privileges required. For instance, if command line shell access is necessary, make sure it is safe, password-protected, and has the lowest user permission level available. The RTOS has a tool for preventing malicious programmes from adversely influencing system performance thanks to the use of privilege levels. All forms of communication should employ IPSec, SSH, SSL, or VPN access as necessary. It is better to presume that all data is sensitive and that data transfer can and will be intercepted.
RTOS network firewall:
Any
device with a network connection should be running with a firewall in place
because modern RTOS include network firewall features. Since embedded devices
are increasingly connected to the same networks as larger size devices,
firewalls are considered standard practise for desktop and server systems. A
firewall is a good first line of defence against network attacks and should
only permit communication through necessary TCP/IP ports. Only ports that are
specifically configured to be open and accessible for connection are permitted
by the firewall, which makes sure that all non-essential ports and services are
shut off.
Conclusion
The security aspect of RTOS needs to be given top
priority because it is utilised in applications and industries where activities
must be done rapidly and without delay. Any security breach to the system could
disrupt operations and have disastrous effects on the environment and human
safety. The security and dependability of safety-critical systems are
examined in-depth and methodically in this essay. In the context of
safety-critical RTOS, we emphasise the best practises, most recent research
initiatives, and their viability. We contrast the solutions qualitatively and
go over their advantages and disadvantages.



Valuable information
ReplyDeleteInformative Article
ReplyDeletenice article
ReplyDeletenice work
ReplyDelete